7.2: Sharing Personal Information
- Last updated
- Save as PDF
- Page ID
- 115954

- Jason S. Wrench, Narissra M. Punyanunt-Carter & Katherine S. Thweatt
- SUNY New Paltz & SUNY Oswego via OpenSUNY
Learning Outcomes
- Describe motives for self-disclosure.
- Appreciate the process of self-disclosure.
- Explain the consequences of self-disclosure.
- Draw and explain the Johari Window.
One of the primary functions of conversations is sharing information about ourselves. In Chapter 2, we discussed Berger and Calabrese’s Uncertainty Reduction Theory (URT).11 One of the basic axioms of URT is that, as verbal communication increases between people when they first meet, the level of uncertainty decreases. Specifically, the type of verbal communication generally discussed in initial interactions is called self-disclosure.12 Self-disclosure is the process of purposefully communicating information about one’s self. Sidney Jourard sums up self-disclosure as permitting one’s “true self” to be known to others.13
As we introduce the concept of self-disclosure in this section, it’s important to realize that there is no right or wrong way to self-disclose. Different people self-disclose for a wide range of different reasons and purposes. Emmi Ignatius and Marja Kokkonen found that self-disclosure can vary for several reasons:14
- Personality traits (shy people self-disclose less than extraverted people)
- Cultural background (Western cultures disclose more than Eastern cultures)
- Emotional state (happy people self-disclose more than sad or depressed people)
- Biological sex (females self-disclose more than males)
- Psychological gender (androgynous people were more emotionally aware, topically involved, and invested in their interactions; feminine individuals disclosed more in social situations, and masculine individuals generally did not demonstrate meaningful self-disclosure across contexts)
- Status differential (lower status individuals are more likely to self-disclose personal information than higher-status individuals)
- Physical environment (soft, warm rooms encourage self-disclosure while hard, cold rooms discourage self-disclosure)
- Physical contact (touch can increase self-disclosure, unless the other person feels that their personal space is being invaded, which can decrease self-disclosure)
- Communication channel (people often feel more comfortable self-disclosing when they’re not face-to-face; e.g., on the telephone or through computer-mediated communication)
As you can see, there are quite a few things that can impact how self-disclosure happens when people are interacting during interpersonal encounters.
Motives for Self-Disclosure
So, what ultimately motivates someone to self-disclose? Emmi Ignatius and Marja Kokkonen found two basic reasons for self-disclosure: social integration and impression management. 15
Social Integration
The first reason people self-disclose information about themselves is simply to develop interpersonal relationships. Part of forming an interpersonal relationship is seeking to demonstrate that we have commonality with another person. For example, let’s say that it’s the beginning of a new semester, and you’re sitting next to someone you’ve never met before. You quickly strike up a conversation while you’re waiting for the professor to show up. During those first few moments of talking, you’re going to try to establish some kind of commonality. Maybe you’ll learn that you’re both communication majors or that you have the same favorite sports team or band. Self-disclosure helps us find these areas where we have similar interests, beliefs, values, attitudes, etc.… As humans, we have an innate desire to be social and meet people. And research has shown us that self-disclosure is positively related to liking.16 The more we self-disclose to others, the more they like us and vice versa.
However, we should mention that appropriate versus inappropriate self-disclosures depends on the nature of your relationship. When we first meet someone, we do not expect that person to start selfdisclosing their deepest darkest secrets. When this happens, then we experience an expectancy violation. Judee Burgoon conceptualized expectancy violation theory as an understanding of what happens when an individual within an interpersonal interaction violates the norms for that interaction.17,18Burgoon’s original expectancy violation theory (EVT) primarily analyzed what happened when individuals communicated nonverbally in a manner that was unexpected (e.g., standing too close while talking). Over the years, EVT has been expanded by many scholars to look at a range of different situations when communication expectations are violated.19 As a whole, EVT predicts that when individuals violate the norms of communication during an interaction, they will evaluate that interaction negatively. However, this does depend on the nature of the initial relationship. If we’ve been in a relationship with someone for a long time or if it’s someone we want to be in a relationship with, we’re more likely to overlook expectancy violations.
So, how does this relate to self-disclosure? Mostly, there are ways that we self-disclose that are considered “normal” during different types of interactions and contexts. What you disclose to your best friend will be different than what you disclose to a stranger at the bus station. What you disclose to your therapist will be different than what you disclose to your professor. When you meet a stranger, the types of self-disclosure tend to be reasonably common topics: your major, sports teams, bands, the weather, etc. If, however, you decide to self-disclose information that is overly personal, this would be perceived as a violation of the types of topics that are normally disclosed during initial interactions. As such, the other person is probably going to try to get out of that conversation pretty quickly. When people disclose information that is inappropriate to the context, those interactions will generally be viewed more negatively.20
From a psychological standpoint, finding these commonalities with others helps reinforce our self-concept. We find that others share the same interests, beliefs, values, attitudes, etc., which demonstrates that how we think, feel, and behave are similar to those around us. Admittedly, it’s not like we do all of this consciously.21
Impression Management
The second reason we tend to self-disclose is to portray a specific impression of who we are as individuals to others. Impression management is defined as “the attempt to generate as favorable an impression of ourselves as possible, particularly through both verbal and nonverbal techniques of self-presentation.”22 Basically, we want people to view us in a specific way, so we communicate with others in an attempt to get others to see us that way. Research has found we commonly use six impression management techniques during interpersonal interactions: self-descriptions, accounts, apologies, entitlements and enhancements, flattery, and favors.23,24,25
Self-Descriptions
The first type of impression management technique we can use is self-descriptions, or talking about specific characteristics of ourselves. For example, if you want others to view you professionally, you would talk about the work that you’ve accomplished. If you want others to see you as someone fun to be around, you will talk about the parties you’ve thrown. In both of these cases, the goal is to describe ourselves in a manner that we want others to see.
Accounts
The second type of impression management is accounts. Accounts “are explanations of a predicamentcreating event designed to minimize the apparent severity of the predicament.”26 According to William Gardner and Mark Martinko, in accounts, “actors may deny events occurred, deny causing events, offer excuses, or justify incidents.”27 Basically, accounts occur when an individual is attempting to explain something that their interactant may already know.
For the purposes of initial interactions, imagine that you’re on a first date and your date has heard that you’re a bit of a “player.” An account may be given to downplay your previous relationships or explain away the rumors about your previous dating history.
Apologies
The third type of impression management tactics is apologies. According to Barry Schlenker, apologies are “are designed to convince the audience that the undesirable event should not be considered a fair representation of what the actor is ‘really like.’”28 An apology occurs when someone admits that they have done something wrong while attempting to downplay the severity of the incident or the outcomes.
Imagine you just found out that a friend of yours told a personal story about you during class as an example. Your friend could offer an apology, admitting that they shouldn’t have told the story, but also emphasize that it’s not like anyone in the class knows who you are. In essence, the friend admits that they are wrong, but also downplays the possible outcomes from the inappropriate disclosure of your story.
Entitlements and Enhancements
The fourth type of impression management tactic is the use of entitlements and enhancements. Entitlements and enhancements are “designed to explain a desirable event in a way that maximizes the desirable implications for the actor.” 29 Primarily, “entitlements are designed to maximize an actor’s apparent responsibility for an event; enhancements are designed to maximize the favorability of an event itself.”30 In this case, the goal is to make one’s self look even better than maybe they actually are.
For our examples, let’s look at entitlements and enhancements separately. For an example of an entitlement, imagine that you’re talking to a new peer in class and they tell you about how they singlehandedly organized a wildly popular concert that happened over the weekend. In this case, the individual is trying to maximize their responsibility for the party in an effort to look good.
For an example of an enhancement, imagine that in the same scenario, the individual talks less about how they did the event single-handedly and talks more about how amazing the event itself was. In this case, they’re aligning themselves with the event, so the more amazing the event looks, the better you’ll perceive them as an individual.
Flattery
The fifth impression management tactic is the use of flattery, or the use of compliments to get the other person to like you more. In this case, there is a belief that if you flatter someone, they will see you in a better light. Imagine there’s a new player on your basketball team. Almost immediately, they start complimenting you on your form and how they wish they could be as good as you are. In this case, the person may be completely honest, but the use of flattery will probably get you to see that person more positively as well.
Favors
The last tactic that researches have described for impression management is favors. Favors “involve doing something nice for someone to gain that person’s approval.” 31 One way that we get others to like us is to do things for them. If we want our peers in class to like us, then maybe we’ll share our notes with them when they’re absent. We could also volunteer to let someone use our washer and dryer if they don’t have one. There are all kinds of favors that we can do for others. Although most of us don’t think of favors as tactics for managing how people perceive us, they have an end result that does.
Social Penetration Theory
In 1973, Irwin Altman and Dalmas Taylor were interested in discovering how individuals become closer to each other.32 They believed that the method of self-disclosure was similar to social penetration and hence created the social penetration theory. This theory helps to explain how individuals gradually become more intimate based on their communication behaviors. According to the social penetration theory, relationships begin when individuals share non-intimate layers and move to more intimate layers of personal information.33
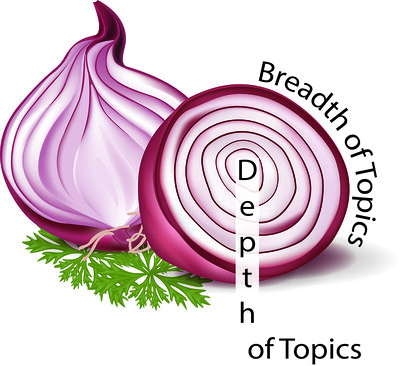
Altman and Taylor believed that individuals discover more about others through self-disclosure. How people comprehend others on a deeper level helps us also gain a better understanding of ourselves. The researchers believe that penetration happens gradually. The scholars describe their theory visually like an onion with many rings or levels.34 A person’s personality is like an onion because it has many layers (Figure 7.2.1). We have an outer layer that everyone can see (e.g., hair color or height), and we have very personal layers that people cannot see (e.g., our dreams and career aspirations). Three factors affect what people chose to disclose. The first is personal characteristics (e.g., introverted or extraverted). The second is the possibility of any reward or cost with disclosing to the other person (e.g., information might have repercussions if the receiver does not like or agree with you). And the third is the situational context (e.g., telling your romantic partner that you want to terminate the relationship on your wedding day).
When people first meet each other, they start from their outer rings and slowly move towards the core. The researchers described how people typically would go through various stages to become closer. The first stage is called the orientation stage, where people communicate on very superficial matters like the weather. The next stage is the exploratory affective stage, where people will disclose more about their feelings about normal topics like favorite foods or movies. Many of our friendships remain at this stage. The third stage is more personal and called the affective stage, where people engage in more private topics. The fourth stage is the stable stage, where people will share their most intimate details. The last stage is not obligatory and does not necessarily happen in every relationship, it is the depenetration stage, where people start to decrease their disclosures.
Social penetration theory also contains two different aspects. The first aspect is breadth, which refers to what topics individuals are willing to talk about with others. For instance, some people do not like to talk about religion and politics because it is considered inappropriate. The second aspect is depth, which refers to how deep a person is willing to go in discussing certain topics. For example, some people don’t mind sharing information about themselves in regards to their favorite things. Still, they may not be willing to share their most private thoughts about themselves because it is too personal. The researchers believe that by self-disclosing to others both in breadth and depth, then it could lead to more relational closeness.
Johari Window
The name “Johari” is a combination of the two researchers who originated the concept: Joseph Luft (Jo) and Harrington Ingham (hari).35 The basic idea behind the Johari Window is that we build trust in our interpersonal relationships as we self-disclose revealing information about ourselves, and we learn more about ourselves as we receive feedback from the people with whom we are interacting. As you can see in Figure 7.2.2, the Johari Window is represented by four window panes. Two window panes refer to ourselves, and two refer to others. First, when discussing ourselves, we have to be aware that somethings about ourselves are known to us, and others are not. For example, we may be completely aware of the fact that we are extraverted and love talking to people (known to self). However, we may not be aware of how others tend to view our extraversion as positive or negative (unknown to self). The second part of the window is what is known to others and unknown to others. For example, some common information known to others includes your height, weight, hair color, etc. At the same time, there is a bunch of information that people don’t know about us: deepest desires, joys, goals in life, etc. Ultimately, the Johari Window breaks this into four different quadrants (Figure 7.2.2)
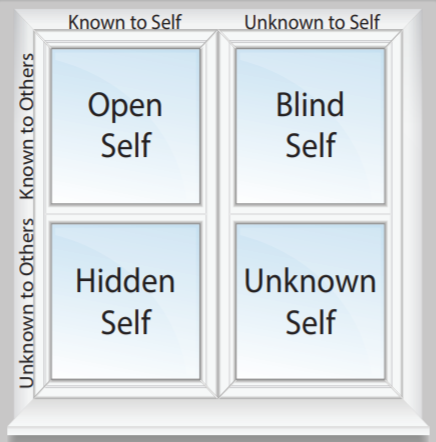
Open Self
The first quadrant of the Johari Window is the open self, or when information is known to both ourselves and others. Although some facets are automatically known, others become known as we disclose more and more information about ourselves with others. As we get to know people and self-disclose and increasingly deeper levels, the open self quadrant grows. For the purposes of thinking about discussions and self-disclosures, the open self is where the bulk of this work ultimately occurs.
Information in the open self can include your attitudes, beliefs, behaviors, emotions/feelings, experiences, and values that are known to both the person and to others. For example, if you wear a religious symbol around your neck (Christian Cross, Jewish Start of David, Islamic Crescent Moon and Star, etc.), people will be able to ascertain certain facts about your religious beliefs immediately.
Hidden Self
The second quadrant is what is known to ourselves but is not known to others. All of us have personal information we may not feel compelled to reveal to others. For example, if you’re a member of the LGBTQIA+ community, you may not feel the need to come out during your first encounter with someone new. It’s also possible that you’ll keep this information from your friends and family for a long time.
Think about your own life, what types of things do you keep hidden from others? One of the reasons we keep things hidden is because it’s hard to open ourselves up to being vulnerable. Typically, the hidden self will decrease as a relationship grows. However, if someone ever violates our trust and discusses our hidden self with others, we are less likely to keep disclosing this information in the future. If the trust violation is extreme enough, we may discontinue that relationship altogether.
Blind Self
The third quadrant is called the blind self because it’s what we don’t know about ourselves that is known by others. For example, during an initial interaction, we may not know how the other person is reacting to us. We may think that we’re coming off as friendly, but the other person may be perceiving us as shy or even pushy. One way to decrease the blind self is by soliciting feedback from others. As others reveal more of our blind selves, we can become more self-aware of how others perceive us.
One problem with the blind self is that how people view us and how we view ourselves can often be radically different. For example, people may perceive you as cocky, but in reality, you’re scared to death. It’s important to decrease the blind self during our interactions with others, because how people view us will determine how they interact with us.
Unknown Self
Lastly, we have the unknown self, or when information is not known by ourselves or others. The unknown self can include aptitudes/talents, attitudes/feelings, behaviors, capabilities, etc. that are unknown to us or others. For example, you may have a natural talent to play the piano. Still, if you’ve never sat down in front of a piano, neither you nor others would have any way of knowing that you have the aptitude/talent for playing the piano. Sometimes parts of the unknown self are just under the surface and will arise with time and in the right contexts, but other times no one will ever know these unknown parts.
One other area that can affect the unknown self involves prior experiences. It’s possible that you experienced a traumatic event that closes you down in a specific area. For example, imagine that you are an amazing writer, but someone, when you were in the fourth grade, made fun of a story you wrote, so you never tried writing again. In this case, the aptitude/talent for writing has been stamped out because of that one traumatic experience as a child. Sadly, a lot of us probably have a range of aptitudes/talents, attitudes/feelings, behaviors, capabilities, etc. that were stopped because of traumas throughout our lives.
Key Takeaways
- We self-disclose to share information with others. It allows us to express our thoughts, feelings, and behaviors.
- Self-disclosure includes levels of disclosure, reciprocity in disclosure, and appropriate disclosure.
- There can be positive and negative consequences of self-disclosure. These consequences can strengthen how you feel or create distance between you and someone else.
- The Johari Window is a model that helps to illustrate self-disclosure and the process by which you interact with other people.
Exercises
- Create a self-penetration diagram for yourself. What topics are you open to talk about? What are you not willing to discuss? Then compare with another student in class. How were you similar or dissimilar? Why do you think these differences/ similarities exist?
- Think of a time when you’ve used the six different impression management techniques. How effective were you with each technique? What could you have done differently?
- Draw your own Johari Window. Fill in each of the window panes with a topic of self-disclosure. You will probably need to ask a close friend or family member to help you with the unknown self pane. Why did you put what you put? Does it make sense? Why?

