10.1.2: The CMC Process
- Last updated
- Save as PDF
- Page ID
- 115903

- Jason S. Wrench, Narissra M. Punyanunt-Carter & Katherine S. Thweatt
- SUNY New Paltz & SUNY Oswego via OpenSUNY
\( \newcommand{\vecs}[1]{\overset { \scriptstyle \rightharpoonup} {\mathbf{#1}} } \)
\( \newcommand{\vecd}[1]{\overset{-\!-\!\rightharpoonup}{\vphantom{a}\smash {#1}}} \)
\( \newcommand{\dsum}{\displaystyle\sum\limits} \)
\( \newcommand{\dint}{\displaystyle\int\limits} \)
\( \newcommand{\dlim}{\displaystyle\lim\limits} \)
\( \newcommand{\id}{\mathrm{id}}\) \( \newcommand{\Span}{\mathrm{span}}\)
( \newcommand{\kernel}{\mathrm{null}\,}\) \( \newcommand{\range}{\mathrm{range}\,}\)
\( \newcommand{\RealPart}{\mathrm{Re}}\) \( \newcommand{\ImaginaryPart}{\mathrm{Im}}\)
\( \newcommand{\Argument}{\mathrm{Arg}}\) \( \newcommand{\norm}[1]{\| #1 \|}\)
\( \newcommand{\inner}[2]{\langle #1, #2 \rangle}\)
\( \newcommand{\Span}{\mathrm{span}}\)
\( \newcommand{\id}{\mathrm{id}}\)
\( \newcommand{\Span}{\mathrm{span}}\)
\( \newcommand{\kernel}{\mathrm{null}\,}\)
\( \newcommand{\range}{\mathrm{range}\,}\)
\( \newcommand{\RealPart}{\mathrm{Re}}\)
\( \newcommand{\ImaginaryPart}{\mathrm{Im}}\)
\( \newcommand{\Argument}{\mathrm{Arg}}\)
\( \newcommand{\norm}[1]{\| #1 \|}\)
\( \newcommand{\inner}[2]{\langle #1, #2 \rangle}\)
\( \newcommand{\Span}{\mathrm{span}}\) \( \newcommand{\AA}{\unicode[.8,0]{x212B}}\)
\( \newcommand{\vectorA}[1]{\vec{#1}} % arrow\)
\( \newcommand{\vectorAt}[1]{\vec{\text{#1}}} % arrow\)
\( \newcommand{\vectorB}[1]{\overset { \scriptstyle \rightharpoonup} {\mathbf{#1}} } \)
\( \newcommand{\vectorC}[1]{\textbf{#1}} \)
\( \newcommand{\vectorD}[1]{\overrightarrow{#1}} \)
\( \newcommand{\vectorDt}[1]{\overrightarrow{\text{#1}}} \)
\( \newcommand{\vectE}[1]{\overset{-\!-\!\rightharpoonup}{\vphantom{a}\smash{\mathbf {#1}}}} \)
\( \newcommand{\vecs}[1]{\overset { \scriptstyle \rightharpoonup} {\mathbf{#1}} } \)
\(\newcommand{\longvect}{\overrightarrow}\)
\( \newcommand{\vecd}[1]{\overset{-\!-\!\rightharpoonup}{\vphantom{a}\smash {#1}}} \)
\(\newcommand{\avec}{\mathbf a}\) \(\newcommand{\bvec}{\mathbf b}\) \(\newcommand{\cvec}{\mathbf c}\) \(\newcommand{\dvec}{\mathbf d}\) \(\newcommand{\dtil}{\widetilde{\mathbf d}}\) \(\newcommand{\evec}{\mathbf e}\) \(\newcommand{\fvec}{\mathbf f}\) \(\newcommand{\nvec}{\mathbf n}\) \(\newcommand{\pvec}{\mathbf p}\) \(\newcommand{\qvec}{\mathbf q}\) \(\newcommand{\svec}{\mathbf s}\) \(\newcommand{\tvec}{\mathbf t}\) \(\newcommand{\uvec}{\mathbf u}\) \(\newcommand{\vvec}{\mathbf v}\) \(\newcommand{\wvec}{\mathbf w}\) \(\newcommand{\xvec}{\mathbf x}\) \(\newcommand{\yvec}{\mathbf y}\) \(\newcommand{\zvec}{\mathbf z}\) \(\newcommand{\rvec}{\mathbf r}\) \(\newcommand{\mvec}{\mathbf m}\) \(\newcommand{\zerovec}{\mathbf 0}\) \(\newcommand{\onevec}{\mathbf 1}\) \(\newcommand{\real}{\mathbb R}\) \(\newcommand{\twovec}[2]{\left[\begin{array}{r}#1 \\ #2 \end{array}\right]}\) \(\newcommand{\ctwovec}[2]{\left[\begin{array}{c}#1 \\ #2 \end{array}\right]}\) \(\newcommand{\threevec}[3]{\left[\begin{array}{r}#1 \\ #2 \\ #3 \end{array}\right]}\) \(\newcommand{\cthreevec}[3]{\left[\begin{array}{c}#1 \\ #2 \\ #3 \end{array}\right]}\) \(\newcommand{\fourvec}[4]{\left[\begin{array}{r}#1 \\ #2 \\ #3 \\ #4 \end{array}\right]}\) \(\newcommand{\cfourvec}[4]{\left[\begin{array}{c}#1 \\ #2 \\ #3 \\ #4 \end{array}\right]}\) \(\newcommand{\fivevec}[5]{\left[\begin{array}{r}#1 \\ #2 \\ #3 \\ #4 \\ #5 \\ \end{array}\right]}\) \(\newcommand{\cfivevec}[5]{\left[\begin{array}{c}#1 \\ #2 \\ #3 \\ #4 \\ #5 \\ \end{array}\right]}\) \(\newcommand{\mattwo}[4]{\left[\begin{array}{rr}#1 \amp #2 \\ #3 \amp #4 \\ \end{array}\right]}\) \(\newcommand{\laspan}[1]{\text{Span}\{#1\}}\) \(\newcommand{\bcal}{\cal B}\) \(\newcommand{\ccal}{\cal C}\) \(\newcommand{\scal}{\cal S}\) \(\newcommand{\wcal}{\cal W}\) \(\newcommand{\ecal}{\cal E}\) \(\newcommand{\coords}[2]{\left\{#1\right\}_{#2}}\) \(\newcommand{\gray}[1]{\color{gray}{#1}}\) \(\newcommand{\lgray}[1]{\color{lightgray}{#1}}\) \(\newcommand{\rank}{\operatorname{rank}}\) \(\newcommand{\row}{\text{Row}}\) \(\newcommand{\col}{\text{Col}}\) \(\renewcommand{\row}{\text{Row}}\) \(\newcommand{\nul}{\text{Nul}}\) \(\newcommand{\var}{\text{Var}}\) \(\newcommand{\corr}{\text{corr}}\) \(\newcommand{\len}[1]{\left|#1\right|}\) \(\newcommand{\bbar}{\overline{\bvec}}\) \(\newcommand{\bhat}{\widehat{\bvec}}\) \(\newcommand{\bperp}{\bvec^\perp}\) \(\newcommand{\xhat}{\widehat{\xvec}}\) \(\newcommand{\vhat}{\widehat{\vvec}}\) \(\newcommand{\uhat}{\widehat{\uvec}}\) \(\newcommand{\what}{\widehat{\wvec}}\) \(\newcommand{\Sighat}{\widehat{\Sigma}}\) \(\newcommand{\lt}{<}\) \(\newcommand{\gt}{>}\) \(\newcommand{\amp}{&}\) \(\definecolor{fillinmathshade}{gray}{0.9}\)Learning Outcomes
- Differentiate between synchronous and asynchronous communication.
- Explain the role of nonverbal cues in computer-mediated communication.
- Describe the various rules and norms associated with computer-mediated communication and their importance to netiquette.
- Examine the human communication factors related to computer-mediated communication.
- Discuss the process and importance of forming impressions online.
As interpersonal communication scholars, our interest in CMC is less about the technologies that people are using and more about how people are using technology to interact with one another. So instead of focusing on how one goes about coding new software, interpersonal communication scholars focus on how new technologies and software help facilitate interpersonal communication. For example, Pat and Sam are playing the latest Massive Multiplayer Online Roleplaying Game (e.g., Word of Warcraft, Fortnite). In Figure 12.2.1 we have two people playing a video game over the together but from different locations. Through a technology called VoIP, Sam and Pat can play video games at the same time while talking to each other through the use of headsets.

Synchronous and Asynchronous Communication
In this section, we’re going to delve more deeply into the areas of synchronous and asynchronous communication. In Figure 12.2.2, Sam and Pat are in some kind of underworld, fiery landscape. Pat is playing a witch character, and Sam is playing a vampire character. The two can coordinate their movements to accomplish in-game tasks because they can talk freely to one another while playing the game in real time. As previously discussed, this type of CMC is synchronous communication, or communication that happens in real time. Conversely, asynchronous communication is the exchange of messages with a time lag. In other words, in asynchronous communication, people can communicate on their own schedules as time permits instead of in real time. For example, Figure 12.2.2 shows a conversation between two college students. In this case, two college students are using SMS, commonly called texting) to interact with each other. The conversation starts at 2:25 PM. The first person initiates the conversation, but doesn’t get a response until 3:05 PM. The third turn in the interaction then doesn’t happen until 5:40 PM. In this exchange, the two people interacting can send responses at their convenience, which is one of the main reasons people often rely on asynchronous communication. Other common forms of asynchronous communication include emails, instant messaging, online discussions, etc….

Now, is it possible for people to use the same SMS technology to interact synchronously? Of course. One of our coauthors remembers two students on a trip who were sitting next to each other and texting backand-forth because they didn’t want their conversation to be overheard by others in the van. Their interaction was clearly mediated, and in real time, so it would be considered synchronous communication.
Nonverbal Cues
One issue related to CMC is nonverbal communication. Historically, most of the media people have used to interact with one another have been asynchronous and text-based, making it difficult to fully ascertain the meaning behind a string of words. Mary J. Culnan and M. Lynne Markus believe that the functions nonverbal behaviors meet in interpersonal interactions simply go unmet in CMC.9 If so, interpersonal communication must always be inherently impersonal when it’s conducted using computer-mediated technologies. This perspective has three underlying assumptions:
- Communication mediated by technology filters out communicative cues found in FtF interaction,
- Different media filter out or transmit different cues, and
- Substituting technology-mediated for FtF communication will result in predictable changes in intrapersonal and interpersonal variables.10
Let’s breakdown these assumptions. First, CMC interactions “filter out” communicative cues found in FtF interactions. For example, if you’re on the telephone with someone, you can’t make eye contact or see their gestures, facial expressions, etc.… If you’re reading an email, you have no nonverbal information to help you interpret the message because there is none. In these examples, the nonverbal cues have been “filtered out” by the media being used. We will revisit this information later in this chapter when we look at a range of theories related to CMC.
Unfortunately, even if we don’t have the nonverbals to help us interpret a message, we interpret the message using our perception of how the sender intended us to understand this message, which is often wrong. How many times have you seen an incorrectly read text or email start a conflict? Of course, one of the first attempts to recover some sense of nonverbal meaning was the emoticon that we discussed earlier in this chapter.
CMC Rules and Norms
As with any type of communication, some rules and norms govern how people communicate with one another. For example, Twitter has an extensive Terms of Service policy that covers a wide range of communication rules. For our purposes here, let’s examine their rules related to hate speech:
Hateful conduct: You may not promote violence against or directly attack or threaten other people on the basis of race, ethnicity, national origin, sexual orientation, gender, gender identity, religious affiliation, age, disability, or serious disease. We also do not allow accounts whose primary purpose is inciting harm towards others on the basis of these categories.
Hateful imagery and display names: You may not use hateful images or symbols in your profile image or profile header. You also may not use your username, display name, or profile bio to engage in abusive behavior, such as targeted harassment or expressing hate towards a person, group, or protected category.11
This statement is an obvious example of a rule that exists on the Twitter platform. Of course, some have argued that these rules are pretty flexible at times, given the type of hateful political speech that is often Tweeted by different political figures.
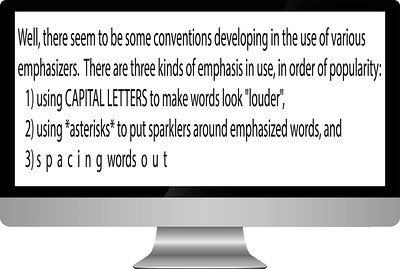
In addition to clearly spelled out rules that govern how people communicate via different technologies, there are also norms. A norm, in this context, is an accepted standard for how one communicates and interacts with others in the CMC environment. For example, one norm by TYPING IN ALL CAPITAL LETTERS, which is considered yelling, people can get frustrated. There’s actually not a consensus on when the use of all caps as a form of yelling first came to be. We do know that newspapers in the 1880s often used all capital letters to emphasize headlines (basically have them jump off the page). At some point in the early 1980s, using all caps as a form of yelling became quite the norm, which was noted in a message post by Dave Decot in 1984 (Figure 12. 2.3).12
In this example, you see three different attempts to create possible systems for emphasizing words. The first is the use of all capital letters for making words seem “louder,” which, as already mentioned, eventually became known as yelling.
Netiquette
Over the years, numerous norms have developed to help individuals communicate in the CMC context. They’re so common that we have a term for them, netiquette. Netiquette is the set of professional and social rules and norms that are considered acceptable and polite when interacting with another person(s) through mediating technologies. Let’s breakdown this definition.
Research Spotlight
In a 2019 study conducted by Jale Ataşalar and Aikaterini Michou, the researchers set out to examine how mindfulness related to problematic Internet use (i.e., Internet addiction). This study was conducted in Ankara, Turkey, and examined 165 Turkish early adolescents (mean age was 13).
To measure mindfulness, the researchers revised the Mindful Attention Awareness
Scale created by Kirk Brown and Richard Ryan.13 The revised scale was used to measure the degree to which individuals engaged in mindful behaviors while online.
Overall, the researchers found that people who were mindful online were less likely to report engaging in problematic Internet use.
Ataşalar, J., & Michou, A. (2019). Coping and mindfulness: Mediators between need satisfaction and generalized problematic Internet use. Journal of Media Psychology, 31(2), 110–115. doi. org/10.1027/1864-1105/a000230
Contexts
First, our definition of netiquette emphasizes that different contexts can create different netiquette needs. Specifically, how one communicates professionally and how one communicates socially are often quite different. For example, you may find it entirely appropriate to say, “What’s up?!” at the beginning of an email to a friend, but you would not find it appropriate to start an email to your boss in this same fashion. Furthermore, it may be entirely appropriate to downplay or disregard spelling errors or grammatical problems in a text you send to a friend, but it is completely inappropriate to have those same errors and problems in a text sent to a professional-client or coworker. One of the biggest challenges many employers have with young employees who are fresh out of college is that they don’t know how to differentiate between appropriate and inappropriate communicative behavior in differing contexts.
This lack of professionalism is also a problem commonly discussed by college and university faculty and staff. Think about the last email you sent to one of your professors? Was this email professional? Did you remember to sign your name? You’d be amazed at the lack of professionalism many college and university faculty and staff see in the emails sent by your peers. Here are some general guidelines for sending professional emails:
- Include a concise, direct subject line.
- Do not mark something as “urgent” unless it really is.
- Begin with a proper greeting (Dear Mr. X, Professor Y:, etc.)
- Double-check your grammar.
- Correct any spelling mistakes.
- Include only essential information. Be concise.
- State your intention clearly and directly.
- Make sure your message is logically organized.
- Be polite and ensure your tone is appropriate.
- Avoid all CAPS or all lowercase letters.
- Avoid “textspeak” (e.g., plz, lol)
- If you want the recipient to do something, make the desired action very clear.
- End with a polite closing (using “please” and “thank you”).
- Do not send an email if you’re angry or upset.
- Edit and proofread before hitting “send.”
- Use “Reply All” selectively (very selectively.
Rules and Norms
Second, our definition of netiquette combines both rules and norms. Part of being a competent communicator in a CMC environment is knowing what the rules are and respecting them. For example, if you know that Twitter’s rules ban hate speech, then engaging in hate speech using the Twitter platform shows a disregard for the rules and would not be considered appropriate behavior. In essence, hate speech is anti-netiquette. We also do not want to ignore the fact that in different CMC contexts, different norms often develop. For example, maybe you’re taking an online course and you’re required to engage in weekly discussions. One common norm in an online class is to check the previously replies to a post before posting your reply. If you don’t, then you are jumping into a conversation that’s already occurred and throwing your two-cents in without knowing what’s happening.
Acceptable and Polite CMC Behavior
Third, netiquette attempts to govern what is both acceptable and polite. Yelling via a text message may be acceptable to some of your friends, but is it polite given that typing in all caps is generally seen as yelling? Being polite shows others respect and demonstrates socially appropriate behaviors.
Mindfulness Activity
If you’ve spent any time online recently, you may have noticed that it can definitely feel like a cesspool. There are many trolls, making the Internet a place where civil interactions are hard to come by. Mitch Abblett came up with five specific guidelines for interacting with others online:
- Be kind and compassionately courteous with all posts and comments.
- No hate speech, bullying, derogatory or biased comments regarding self, others in the community, or others in general.
- No Promotions or Spam.
- Do not give mental health advice.
- Respect everyone’s privacy and be thoughtful in the nature and depth of your sharing.14
Think about your interactions with others in the online world. Have you ever communicated with others without considering whether your own intentions and attitude are appropriate?
Online Interaction
Fourth, our definition involves interacting with others. This interaction can be one-on-one, or this interaction can be one-to-many. The first category, one-on-one, is more in the wheelhouse of interpersonal communication. Examples include sending a text to one person, sending an email to one person, talking to one person via Skype or Zoom, etc. The second category, one-to-many, requires its own set of rules and norms. Some examples of common one-to-many CMC could include engaging in a group chat via texting, “replying all” to an email received, being interviewed by a committee via Skype, etc. Notice that our examples for one-to-many involve the same technologies used for one-on-one communication.
Range of Mediating
Technologies Lastly, netiquette can vary based on the different types of mediating technologies. For example, it may be considered entirely appropriate for you to scream, yell, and curse when your playing with your best friend on Fortnite, but it wouldn’t be appropriate to use the same communicative behaviors when engaging in a video conference over Skype. Both technologies use VoIP, but the platforms and the contexts are very different, so they call for different types of communicative behaviors. Some differences will exist in netiquette based on whether you’re in an entirely text-based medium (e.g., email, texting) or one where people can see you (e.g., Skype, WebEx, Zoom). Ultimately, engaging in netiquette requires you to learn what is considered acceptable and polite behavior across a range of different technologies.
Communication Factors
Communication factors are an essential part of understanding how computer-mediated communication impacts interpersonal relationships. In this section, we’re going to examine two specific communication factors that have been researched in a variety of CMC contexts: communication apprehension and impression formation.
Communication Apprehension
Most of the research examining CA and CMC started at the beginning of the 21st Century. Until 1996 when America Online (AOL) provided unlimited access to the Internet for a low monthly fee, most people did not have access to the Internet because of the cost. It wasn’t until the public became more actively involved in interacting through technology that communication scholars became interested in communication traits related to CMC. One early study conducted by Scott W. Campbell and Michael R. Neer investigated whether an individual’s level of communication apprehension (CA) could predict how they felt about CMC.15 In the study, the authors predicted that an individual’s level of CA could predict whether the individuals believed that CMC was an effective medium for interpersonal communication; however, the researchers did not find a significant relationship. Furthermore, the researchers found that there wasn’t a significant relationship between CA and people’s satisfaction with their CMC experiences. Here’s how the researchers attempted to make sense of these findings:
One plausible interpretation is that high apprehensives simply do not view CMC positively or negatively. Yet, they recognize that it reduces the threat posed to them in FtF settings. An equally plausible explanation is that high apprehensives do not regard CMC as an interpersonal obstacle to overcome because it is not FtF, but a substitute that fails to challenge or override their apprehension level.16
Jason S. Wrench and Narissra M. Punyanunt-Carter furthered the inquiry into CA and CMC by exploring how people reacted to different types of CMC. Specifically, Wrench and Punyanunt-Carter were interested in examining email CA, online chatting CA, and instant messaging CA. You can see the measures that Wrench and Punyanunt-Carter created for this study in Table 12.2.1. It’s important to emphasize that the technologies listed in Table 12.2.1 here were the technologies most commonly used by the public when this study was conducted in the mid-2000s.
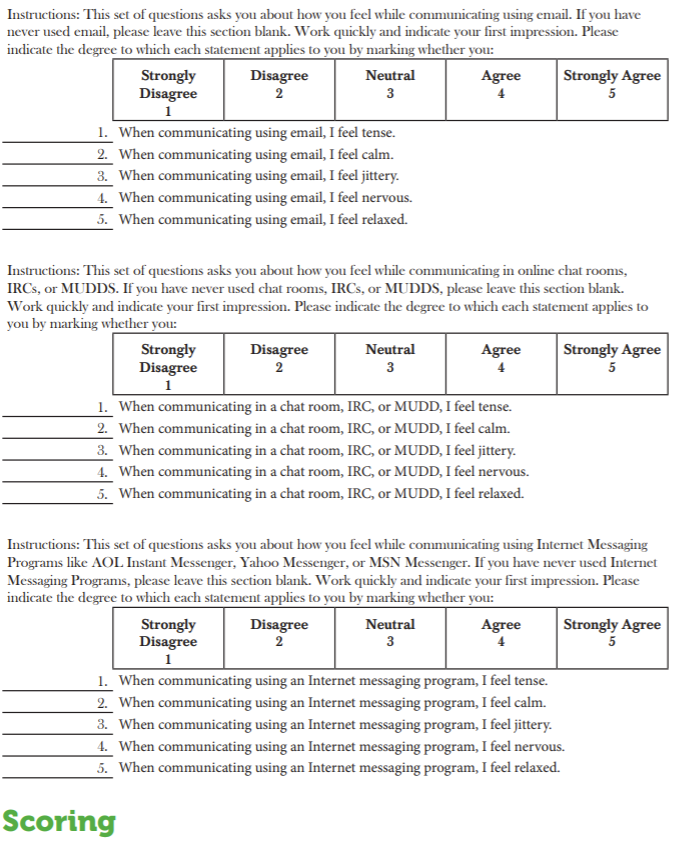 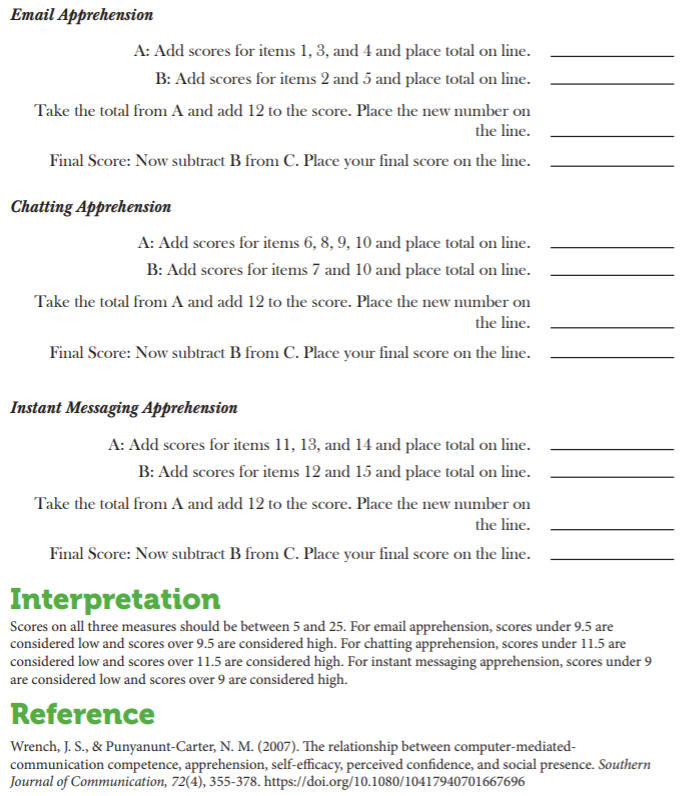 |
In addition to CMCA, Wrench and Punyanunt-Carter were also interested in an individual’s skill levels with CMC. CMC skill was defined as three distinct concepts: computer efficacy (individuals’ confidence in using a computer), Internet efficacy (individuals’ confidence in using the Internet), and CMC competence. Brian H. Spitzberg believed that CMC competence consisted of three important factors: 1) people must be motivated to interact with others competently, 2) people must possess specialized knowledge and technical know-how, and 3) people must learn the rules and norms for communicating in the CMC context.17 Wrench and Punyanunt-Carter found that CMCA was negatively related to computer efficacy, Internet efficacy, and CMC competence.
In a subsequent study by Daniel Hunt, David Atkin, and Archana Krishnan, the researchers set out to examine CMCA and Facebook interactions, using a revised version of the Wrench and PunyanuntCarter CMCA scales to measure Facebook CA.18 The study showed that CMCA decreased one’s motivation to use Facebook as a tool for interpersonal communication. These findings were similar to those of Narissra M. Punyanunt-Carter, J. J. De La Cruz, and Jason S. Wrench, who examined CMCA on the social media app Snapchat.19 In this study, the researchers examined CMCA with regards to satisfying a combination of both functional and entertainment needs. Functional needs were defined as needs that drive an individual to accomplish something (e.g., feel less lonely, solve a problem, meet new people, decision making). Entertainment needs were defined as needs that allow an individual to keep her/him/themselves occupied (e.g., because it’s fun, because it’s convenient, communicate easily). In this study, Punyanunt-Carter, De La Cruz, and Wrench found that individuals with high levels of Snapchat CA were more likely to use Snapchat for functional purposes than for entertainment purposes.
In a second study conducted by Punyanunt-Carter, De La Cruz, and Wrench, the researchers set out to examine social media CA in relation to introversion, social media use, and social media addiction.20 In this study, the researchers found that social media CA was positively related to introversion, which is in line with previous research examining CA and introversion. Furthermore, introversion was negatively related to social media use, but social media CA was not related to social media use. Lastly, both social media CA and introversion were negatively related to social media addiction. Overall, this shows that individuals with social media CA are just not as likely to use social media, so they’re less likely to become addicted to it.
So, what does all of this tell us? From our analysis of CA and CMC, we’ve come to understand that people with high levels of CA tend to function better in a CMC environment than in a FtF one, they’re still less likely to engage in CMC as compared to those people with low levels of CMCA. People with low levels of CMCA just see CMC as another platform for communication.
Online Impression Formation
In the 21st Century, so much of what we do involves interacting with people online. How we present ourselves to others through our online persona (impression formation) is very important. How we communicate via social media and how professional our online persona is can be a determining factor in getting a job.
It’s important to understand that in today’s world, anything you put online can be found by someone else. According to the 2018 CareerBuilder.com social recruiting survey, a survey of more than 1,000 hiring managers, 70% admit to screening potential employees using social media, and 66% use search engines to look up potential employees.21 In fact, having an online persona can be very beneficial. Forty-seven percent of hiring managers admit to not calling a potential employee when the employee does not have an online presence. You may be wondering what employers are looking for when they check out potential employees online. The main things employers look for are information to support someone’s qualifications (58%), whether or not an individual has a professional online persona (50%), to see what others say about the potential candidate (34%), and information that could lead a hiring manager to decide not to hire someone (22%).22 According to CareerBuilder.com, here are the common reasons someone doesn’t get a job because of her/his/their online presence:
- Job candidate posted provocative or inappropriate photographs, videos or information: 40 percent
- Job candidate posted information about their alcohol of drug use: 36 percent
- Job candidate made discriminatory comments related to race, gender, religion, etc.: 31 percent
- Job candidate was linked to criminal behavior: 30 percent • Job candidate lied about qualifications: 27 percent
- Job candidate had poor communication skills: 27 percent
- Job candidate bad-mouthed their previous company or fellow employee: 25 percent
- Job candidate’s screen name was unprofessional: 22 percent
- Job candidate shared confidential information from previous employers: 20 percent
- Job candidate lied about an absence: 16 percent
- Job candidate posted too frequently: 12 percent23
As you can see, many organizations believe that what you put online says a lot about you as a person, so they are checking the Internet for information. If what you have online is inappropriate, it may prevent you from getting hired, but fortunately, what you have online can also help get you hired. The same CareerBuilder.com study found that 57% of hiring managers have found information about a candidate online that has solidified their decision to hire that person. Here is a list of what hiring managers found that made them want to hire someone:
- Job candidate’s background information supported their professional qualifications for the job: 37 percent
- Job candidate was creative: 34 percent
- Job candidate’s site conveyed a professional image: 33 percent
- Job candidate was well-rounded, showed a wide range of interests: 31 percent
- Got a good feel for the job candidate’s personality, could see a good fit within the company culture: 31 percent
- Job candidate had great communications skills: 28 percent
- Job candidate received awards and accolades: 26 percent
- Other people posted great references about the job candidate: 23 percent
- Job candidate had interacted with company’s social media accounts: 22 percent
- Job candidate posted compelling video or other content: 21 percent
- Job candidate had a large number of followers or subscribers: 18 percent24
As you can see, having an online presence is important in the 21st Century. Some people make the mistake of having no social media presence, which can backfire. In today’s social media society, having no online presence can look very strange to hiring managers. You should consider your social media presence as an extension of your resume. At the very least, you should have a profile on LinkedIn, the social networking site most commonly used by corporate recruiters.25
Research Spotlight
Mikaela Pitcan, Alice E. Marwick, and Danah Boyd set out to explore how young people of low socioeconomic status handled issues of privacy and presentation in social media. The researchers interviewed 28 young adults who considered themselves to be upwardly mobile. The researchers found two general themes through their interviews: respectability tactics and judgments of female sexuality.
First, the researchers found that the participants “self-censored in a manner they described as presenting a ‘neutral’ or ‘vanilla’ face, catering to the respectability norms of the most powerful potential viewers—often potential employers or highstatus community members—rather than peers.”26 The participants realized that having a social media presence was important, but they also knew that others could judge their social media use, so they were cognitively aware of what they posted. Furthermore, the participants were cognizant that their social media use today could be read by others in the future, so they had to consider a long-term perspective when it came to appropriateness online.
Second, there was a pattern of judging females’ use of social media in sexually explicit ways. When it came to respectably presenting one’s self online, women were judged more harshly for their inclusion of sexually themed posts.
Pitcan, M., Marwick, A. E., & Boyd, D. (2018). Performing a vanilla self: Respectability politics, social class, and the digital world. Journal of Computer-Mediated Communication, 23(3), 163-179. doi.org/10.1093/jcmc/zmy008
Co-Present Interactions and Mediated Communication
For this discussion, we need to focus on the idea of co-present interactions, in which people are physically occupying the same space while interacting with one another. Historically, most interpersonal communication has involved co-present interactions, but with the advent of a range of communication technologies, people no longer have to be co-present to interact. On the flip side, there are many people who are co-present but use technology as a way of avoiding FtF interactions with those around them. One of our professor friends recently remarked, “when I started my career, I always had to tell students to quiet down at the beginning of class. Now, they’re already quiet because they’re all looking at their cellphones ignoring those around them.”
Now we often have to encourage collocated social interactions, and we wonder how we can get people sitting next to each other to talk to one another. Thomas Olsson, Pradthana Jarusriboonchai, Paweł Woźniak, Susanna Paasovaara, Kaisa Väänänen, and Andrés Lucero argue that there are two basic communication problems facing people today, “(1) the use of current technology disrupting ongoing social situations, and (2) lack of social interaction in collocated situations where it would be desirable.”27 When people don’t interact with one another, they tend to become more socially isolated and lonely, which can lead to a feeling of disengagement with those around them.
How many times have you seen people eating out together yet spending the entire time on their smartphones? Many people believe that this type of multitasking actually enhances productivity, but research tends to disagree with this notion. One study actually demonstrated that when people are confronted with constant distractions like phones ringing or email alerts chiming on a smartphone, people lose an average of 10 IQ points due to these distractions.28 This drop in IQ is equivalent to missing an entire night of sleep. Furthermore, those generations that have grown up with technology are more likely to engage in multitasking behavior.29 In a 2014 study conducted by Jonathan Bowman and Roger Pace, the researchers tested the impact of cell phone usage vs. FtF conversations while performing a complex cognitive task.30 Not surprisingly, individuals who interacted via cell phones were less adept at performing the task than those engaged in FtF interactions. Furthermore, individuals involved in the FtF interactions were more satisfied with their interactions than their peers using a cellphone. The authors of the article also found that, “People think they are effectively communicating their message while dual-tasking even though they are not.”31
So how can technology benefit social interactions? In the Olsson et al. study, the researchers examined several different studies that were designed to help foster collocated social interactions.32 Table 12.2.2 from the Olsson et al. illustrates the basic findings from their study.
| Role of Technology | Social Design Objectives | Design Approaches |
|---|---|---|
| Enable (previous work beyond which the reviewed literature explores) | ||
| Facilitate |
|
|
| Invite |
|
|
| Encourage |
|
|
In Table 12.2.2 you are introduced to four different ways that technology can help facilitate collocated social interaction. You are also presented with the design objectives for each of these different ways to encourage collocated social interaction along with specific design approaches that technology creators can use to help foster collocated social interaction. Let’s look at each of these in turn.
Enabling
First, “enabling interaction refers to the role of a technological artifact making it possible or allowing for social interaction to take place.”33 The goal of enabling is to set up situations where collocated social interaction is possible. As such, there’s less information about specific design objectives and approaches even though most of the research in the area of helping people interact has historically focused on enabling.
Facilitating
Second, “facilitating interaction refers to making it easier to converse, collaborate or otherwise socially interact, or to support desirable feelings, equality or suitable interaction dynamics while doing so.”34 The goal of facilitating collocated social interactions is to help ease tension and encourage people to interact while minimizing possible negative experiences people may face. One of the ways to achieve facilitating is to have an open space for a shared activity. For example, an online college or university may have coffee shop nights or alumni events in various cities. The alumni events don’t necessarily have specific agendas, but the goal is to provide a space where people can meet and interact.
Inviting
Third, “inviting interaction is about the role of informing people of the available proximal social possibilities, which can motivate to spontaneously engage in new encounters.”35 In this case, the focus is on providing people the ability to invite social interaction or respond to invitations to engage in social interaction. One of the best examples of this type of use of technology to help facilitate collocated social interaction is https://www.meetup.com/. Meetup provides a range of different activities and groups people can join that then meet up in the real-world. For example, in the next 24 hours, there is a Swing Dance Cruise, Writer’s Group, and Meditation Workshop I could go to just in my local area.
Encouraging
Lastly, “encouraging interaction is about incentivizing or persuading people to start interacting or maintaining ongoing interaction.”36 In the case of encouraging, it’s not just about providing opportunities, but also using technology to help nudge people into collocated social interaction. For example, an application could require students in an online class who live near each other to get together to study or work on a course project together. You may notice that the common design approach here is introducing constraints. This means that people are required to meet up and engage in collocated social interaction to accomplish a task because neither can do it on their own. Video games have been using a version of this for years. In many social video games, a single player will not have all of the abilities, skills, weapons, etc. to accomplish a specific goal on their own. They must work with other players to accomplish a task. The only difference here is that the tasks are being completed in a FtF context instead of a mediated context.
Key Takeaways
- Synchronous communication is communication that happens in real time, whereas asynchronous communication has a time lag between the exchange of messages.
- Nonverbal behaviors are not inherent in many forms of computer-mediated communication. With text-based messages (email, texts, IRC, etc.), there are no nonverbal cues to attend to at all. In other mediated forms (e.g., Skype, Facetime, Zoom), we can see the other person, but it’s still not the same as an interaction in a FtF context.
- Netiquette is the set of professional and social rules and norms for acceptable and polite behaviors when interacting with another person(s) through mediating technologies.
- A number of human communication variables have been examined within the CMC context: communication apprehension, communication competence, etc.
Exercises
- Think about the asynchronous and synchronous computer-mediated communication technologies you use regularly. Are nonverbal behaviors filtered in or out? How does this impact your ability to understand the other person?
- Have you ever violated netiquette while interacting with other people? What happened? How did other people react?
- Take a few minutes to Google yourself and see what information is easily available about you on the Internet. You may need to try a couple of variations of your name and even add your hometown if your name is very common. If you find information about yourself, how could a potential employer react to that information? Do you need to clean up your Internet profile? Why?

