10.1.3: Taking the Self Online
- Last updated
- Save as PDF
- Page ID
- 115904

- Jason S. Wrench, Narissra M. Punyanunt-Carter & Katherine S. Thweatt
- SUNY New Paltz & SUNY Oswego via OpenSUNY
Learning Outcomes
- Explain Erik Erikson’s conceptualization of identity.
- Describe how Erving Goffman’s theory can help us explain online identities.
- Discuss the three types of online identities described by Andrew F. Wood and Matthew J. Smith
In Chapter 3, we discussed the world of intrapersonal communication. At the beginning of Chapter 3 chapter, we had you describe yourself by answering the question, “Who am I?” 20 different times. Look back at that list. Now, think about yourself in the CMC context. Are you the same person in a FtF interaction as you are in a CMC interaction? Maybe, but maybe not. For example, maybe you’re a very shy person in FtF interactions, and likewise you have problems talking with complete strangers online. However, maybe you’re a very quiet person in FtF interactions, but when you’re playing World of Warcraft, you suddenly become very loud and boisterous. One of the beautiful things about CMC for many people is that they can be almost anyone or anything they want to be online. In this section, we’re going to examine some specific factors related to one’s online self: identity, personality traits, communication traits, privacy, anonymity, and trust.
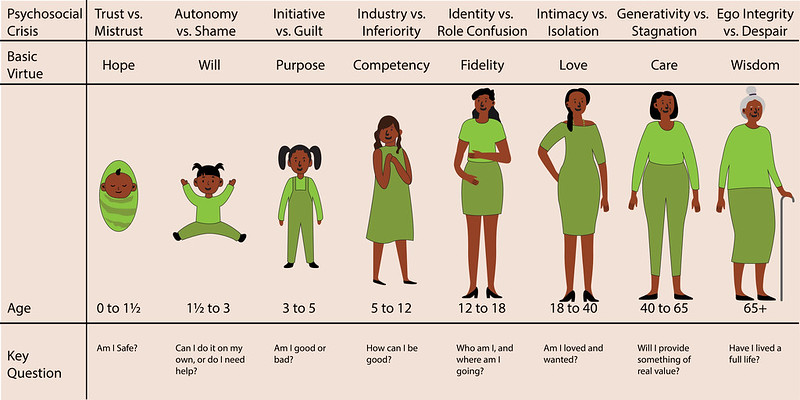
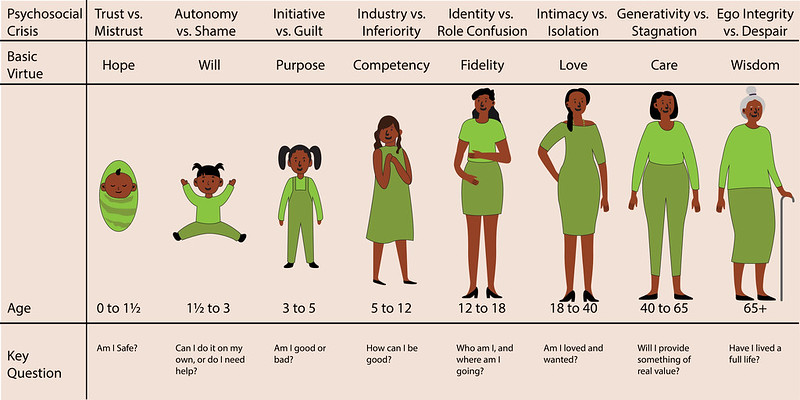
Erik Erikson
Many social psychologists over the years have attempted to define and conceptualize what is meant by the term “identity.” One of the more prominent contributors to this endeavor was Erik Erikson. Erikson believed that an individual’s identity was developed through a series of stages of psychosocial development that occur from infancy to adulthood. At each of the different stages, an individual faces various crises that will influence her/his/their identity positively or negatively. Each crisis pits the psychological needs of the individual against the larger needs of society, which is why these crises are psychosocial in nature. You can see these stages, the crises that occur, the basic virtues associated with the crises, and the central question that is asked at each stage in Figure 12.3.1.37
Our question then, is how does technology impact an individual’s identity development? To answer this question, we need to understand Erikson’s concept of “pseudospeciation,” or the tendency of humans to try to differentiate themselves from other humans.38 Basically, we create in-groups (groups to which we belong) and out-groups (groups to which we do not belong). As Erikson explained, humans have a need “to feel that they are of some special kind (tribe or nation, class or caste, family, occupation, or type), whose insignia they will wear with vanity and conviction, and defend (along with the economic claims they have staked out for their kind) against the foreign, the inimical, the not-so-human kinds.”39 This need to differentiate ourselves from others is especially prominent in those individuals who are under 18 years of age.40
Millennials came of age during the influx of new technologies associated with Web 2.0. Subsequent generations have grown up with technology from birth. Ever seen a baby using an iPad? It happens. Erikson died the same year as the first major Web browser, Netscape, came on the market. Obviously, he did not have anything to say about the influx of technology and identity formation specifically. However, he had seen the invention of other technologies and how they had impacted identity formation, specifically movies:
“interspersed with close-ups of violence and sexual possession and all this without making the slightest demand on intelligence, imagination, or effort. I am pointing here to a widespread imbalance in adolescent experience because I think it explains new kinds of adolescent outbursts and points to new necessities of mastery.”41
Avi Kay believes that today’s social media and other technologies are even more impactful than movies were in Erikson’s day:
An argument can certainly be made that the immediacy, pervasiveness, and intensity of the ideas and images afforded by the advent of movies pale compared to those of the Internet and social media. As such, reactions to those ideas and images via the Internet can only be expected to provoke even greater passions than those Erikson observed among the youth of his generation.42
Kay specifically discusses how the Internet is being used as a tool to radicalize young people in Islamic countries, and the same is also true of many young people in the United States who are radicalized through the Internet into hate groups here. The Internet is a fantastic tool, but the types of information that it can expose an adolescent to during their formative years can send them on a prosocial or antisocial path. Thankfully, there is hope. As Erikson said, “There is no reason to insist that a technological world, as such, need weaken inner resources of adaptation, which may, in fact, be replenished by the goodwill and ingenuity of a communicating species.”43 Although many forces try to sway adolescents towards anti-social behavior and ideologies, technology isn’t inherently bad for identity formation. Technology can also be used to help forge positive identities.
Your Online Identity
We just discussed how an individual’s identity could be shaped by her/his/their interaction with technology, but what about the identity we display when we’re online. In the earliest days of the Internet, it was common for people to be completely anonymous on the Internet (more on this shortly). For our purposes, it’s important to realize that people often present themselves differently in CMC contexts. For example, someone chatting with a complete stranger on Tinder but completely differently when texting with her/his/their mother.
Erving Goffman and Identity
Erving Goffman, in his book The Presentation of Self in Everyday Life, was the first to note that when interacting with others, people tend to guide or control the presentation of themselves to the other person.44 As people, we can alter how we look (to a degree), how we behave, and how we communicate, and all of these will impact the perception that someone builds of us during an interaction. And while we’re attempting to create an impression of ourselves, the other person is also attempting to create a perception of who you are as a person.
In an ideal world, we hope how we’re presenting ourselves will be how the other person interprets this self-presentation, but it doesn’t always work out that way. Goffman coined the term dramaturgical analysis to describe this type of interactive sensemaking because he saw the faces people put on when interacting with others as similar to the roles actors play onstage. In this respect, Goffman used the term “front stage” to the types of behavior we exhibit when we know others are watching us (e.g., an interpersonal interaction). “Backstage” then is the behavior we engage in when we have no audience present, so we are free from the rules and norms of interaction that govern our day-to-day interactions with others. Basically, when we are alone, we can let our hair down and relax by getting out of the character we perform on stage. At the same time, we also prepare for future interactions on stage while we’re backstage. For example, maybe a woman will practice a pick up line she plans on using in a bar after work, or a man will rehearse what he’s going to say when he meets his boyfriend’s parents at dinner that night.
Erving Goffman died in 1982 well before the birth of the WWW and the Internet as most of us know it today, so he didn’t write about the issue of online identities. Syed Murtaza Alfarid Hussain applied Goffman’s dramaturgical approach to Facebook.45 Alfarid Hussain argues that Facebook can be seen as part of the “front stage” for interaction where we perform our identities. As such, Facebook “provides the opportunity for individuals to use props such as user profile information, photo posting/sharing/tagging, status updates, ‘Like’ and ‘Unlike’ others posts, comments or wall posts, profile image/cover page image, online befriending, group/community membership, weblinks and security and privacy settings.”46 If you’re like us, maybe you sat in front of your smartphone, tablet computer, laptop, or desktop computer and wanted to share a meme, but realized that many people you’re friends with on Facebook wouldn’t find the meme humorous, so you didn’t share the meme. When you do this, you are negotiating your identity on stage. You are determining and influencing how others will view you through the types of posts you make, the shares you make, and even the likes you give to others’ posts.
In a study examining identity in blogging and the online 3D multiverse SecondLife, Liam Bullingham and Ana C. Vasconcelos found that most people who blog and those who participated on SecondLife (in their study) “were keen to re-create their offline self online. This was achieved by creating a blogging voice that is true to the offline one, and by publishing personal details about the offline self online, or designing the avatar to resemble the offline self in SL, and in disclosing offline identity in SL.”47 In “Goffman-speak,” people online attempt to mimic their onstage performances across different mediums. Now clearly, not everyone who blogs and hangs out in SecondLife will do this, but the majority of the individuals in Bullingham and Vasconcelos’ study did. The authors noted differences between bloggers and SL users. Specifically, SL users have:
more obvious options to deviate from the offline self and adopt personae in terms of the appearance of the 3D avatar. In blogging, it is perhaps expected that persona adoption does not occur, unless a detachment from the offline self is obvious, such as in the case of pseudonymous blogging. Also, the nature of interaction is different, with blogging resembling more closely platform performances and the SL environment offering more opportunities for contacts and encounters.48
Types of Online Identities
Unlike traditional FtF interactions, online interactions can blur identities as people act in ways impossible in FtF interaction. Andrew F. Wood and Matthew J. Smith discussed three different ways that people express their identities online: anonymous, pseudonymous, and real life (Figure 12.3.2).49
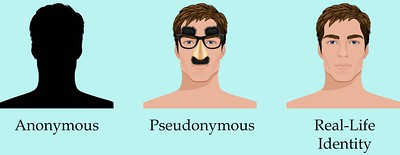
Anonymous Identity
First, people in a CMC context can behave in a way that is completely anonymous. In this case, people in CMC interactions can communicate in a manner that conceals their actual identity. Now, it may be possible for some people to figure out who an anonymous person is (e.g., the NSA, the CIA), but if someone wants to maintain her or his anonymity, it’s usually possible to do so. Think about how many fake Facebook, Twitter, Tinder, and Grindr accounts exist. Some exist to try to persuade you to go to a website (often for illicit purposes like hacking your computer), while others may be “catfishing” for the fun of it.
Catfishing is a deceptive activity perpetrated by Internet predators when they fabricate online identities on social networking sites to lure unsuspecting victims into an emotional/romantic relationship. In the 2010 documentary Catfish, we are introduced to Yaniv “Nev” Schulman, a New York-based photographer, who starts an online relationship with an 8-year-old prodigy named Abby via Facebook. Over the course of nine months, the two exchange more than 1,500 messages, and Abby’s family (mother, father, and sister) also become friends with Nev on Facebook. Throughout the documentary, Nev and his brother Ariel (who is also the documentarian) start noticing inconsistencies in various stories that are being told. Music that was allegedly created by Abby is found to be taken from YouTube. Ariel convinces Nev to continue the relationship knowing that there are inconsistencies and lies just to see how it will all play out. The success of Catfish spawned a television show by the same name on MTV.
From this one story, we can easily see the problems that can arise from anonymity on the Internet. Often behavior that would be deemed completely inappropriate in a FtF encounter suddenly becomes appropriate because it’s deemed “less real” by some. One of the major problems with online anonymity has been cyberbullying. Teenagers today can post horrible things about one another online without any worry that the messages will be linked back to them directly. Unlike FtF bullying victims who leave the bullying behind when they leave school, teens facing cyberbullying cannot even find peace at home because the Internet follows them everywhere. In 2013 12-year-old Rebecca Ann Sedwick committed suicide after being the perpetual victim of cyberbullying through social media apps on her phone. Some of the messages found on her phone after her suicide included, “Why are you still alive?” and “You haven’t killed yourself yet? Go jump off a building.” Rebecca suffered this barrage of bullying for over a year and by around 15 different girls in her school. Sadly, Rebecca’s tale is one that is all too familiar in today’s world. Nine percent of middle-school students reported being victims of cyberbullying, and there is a relationship between victimization and suicidal ideation.50
It’s also important to understand that cyberbullying isn’t just a phenomenon that happens with children. A 2009 survey of Australian Manufacturing Workers’ Union members, found that 34% of respondents faced FtF bullying, and 10.7% faced cyberbullying. All of the individuals who were targets of cyberbullying were also bullied FtF.51
Many people prefer anonymity when interacting with others online, and there can be legitimate reasons to engage in online interactions with others. For example, when one of our authors was coming out as LGBTQIA+, our coauthor regularly talked with people online as they melded the new LGBTQIA+ identity with their Southern and Christian identities. Having the ability to talk anonymously with others allowed our coauthor to gradually come out by forming anonymous relationships with others dealing with the same issues.
Pseudonymous Identity
The second category of interaction is pseudonymous. Wood and Smith used the term pseudonymous because of the prefix “pseudonym”: “Pseudonym comes from the Latin words for ‘false’ and ‘name,’ and it provides an audience with the ability to attribute statements and actions to a common source [emphasis in original].”52 Whereas an anonym allows someone to be completely anonymous, a pseudonym “allows one to contribute to the fashioning of one’s own image.”53
Using pseudonyms is hardly something new. Famed mystery author Agatha Christi wrote over 66 detective novels, but still published six romance novels using the pseudonym Mary Westmacott. Bestselling science fiction author Michael Crichton (of Jurassic Park fame), wrote under three different pseudonyms (John Lange, Jeffery Hudson, and Michael Douglas) when he was in medical school. Even J. K. Rowling (of Harry Potter fame) used the pseudonym Robert Galbraith to write her follow-up novel to the series, The Cuckoo’s Calling (2013). Rowling didn’t want the media hype or inflated reader expectations while writing her follow-up novel. Unfortunately for Rowling, the secret didn’t stay hidden very long.
There are many famous people who use pseudonyms in their social media: @TheTweetOfGod (comedy writer and Daily Show producer, David Javerbaum), @pewdiepie (online personality and producer Felix Arvid Ulf Kjellberg), @baddiewinkle (Octogenarian fashionista and online personality Helen Van Winkle), @doctor.mike (family practitioner and internet celebrity Dr. Mike Varshavski), and more. Some of these people used parts of their real names, and others used fully pseudonymous names. All of them have enormous Internet followings and have used their pseudonyms to build profitable brands. So, why do people use a pseudonym?
The veneer of the Internet allows us to determine how much of an identity we wish to front in online presentations. These images can range from a vague silhouette to a detailed snapshot. Whatever the degree of identity presented, however, it appears that control and empowerment are benefits for users of these communication technologies.”54
Some people even adopt a pseudonym because their online actions may not be “on-brand” for their day-job or because they don’t want to be fully exposed online.
Real Life Identity
Lastly, some people have their real-life identities displayed online. You can find JasonSWrench on Facebook, Instagram, Snapchat, Twitter, LinkedIn, etc…. Our coauthor made the decision to have his social networking site behavior very public from the beginning. Part of the reason was that when he first joined Facebook in 2007, he was required to use his professional school email address that ended with. edu. In the early days, only people with.edu email addresses could join Facebook. Jason also realizes that this behavior is a part of his professional persona, so he doesn’t put anything on one of these sites he wouldn’t want other professionals (or even you) to see and read. When it comes to people in the public eye, most of them use some variation of their real names to enhance their brands. That’s not to say that many of these same people don’t have multiple online accounts, some of which may be completely anonymous or even pseudonymous.
Key Takeaways
- Erikson believed that an individual’s identity is developed through a series of stages of psychosocial development that occur from infancy to adulthood. At each stage, we face a different set of crises that pits an individual’s psychological needs versus the larger societal needs. Part of this development is impacted by the introduction of new technologies, which can be both good for society and problematic.
- Erving Goffman in his book The Presentation of Self in Everyday Life, uses the term “front stage” to describe the types of behavior we exhibit when we know others are watching us (e.g., an interpersonal interaction), and he uses the term “backstage” to refer to behavior we engage in when we have no audience present, so we are free from the rules and norms of interaction that govern our day-to-day interactions with others.
- Andrew F. Wood and Matthew J. Smith discussed three specific types of online identities that people can formulate: anonymous (the person behind a message is completely unknown), pseudonymous (someone uses a pseudonym, but people often know who the real person behind the message is), and real life (when our online and FtF identities are the same).
Exercises
- Of the two theoretical approaches to identity (Erikson and Goffman), which do you think is the better tool for explaining how your online identity and offline identity were formed? Why?
- When it comes to your online CMC behavior, do you have an anonymous, pseudonymous, and real-life identity? How are these similar? How are they different?

